Email remains one of the most widely used communication channels in both personal and professional environments - and that’s exactly why cybercriminals continue to exploit it. From phishing scams to business email compromise (BEC) attacks, malicious actors are becoming increasingly sophisticated in their manipulation of users into clicking on harmful links or sharing sensitive information.
Understanding how these tactics work is crucial for individuals, enterprises, and cybersecurity leaders seeking to mitigate risk and enhance digital resilience.
Why Email-Based Attacks Are Still So Effective
Despite advancements in cybersecurity technologies, email remains a primary attack vector. Cybercriminals rely on human psychology rather than just technical vulnerabilities. They exploit urgency, fear, curiosity, and trust to trigger quick, unverified actions.
Common attack goals include:
- Stealing login credentials
- Gaining access to corporate systems
- Distributing malware or ransomware
- Initiating fraudulent financial transactions
Even well-trained professionals can fall victim when attacks are carefully crafted and contextually relevant.
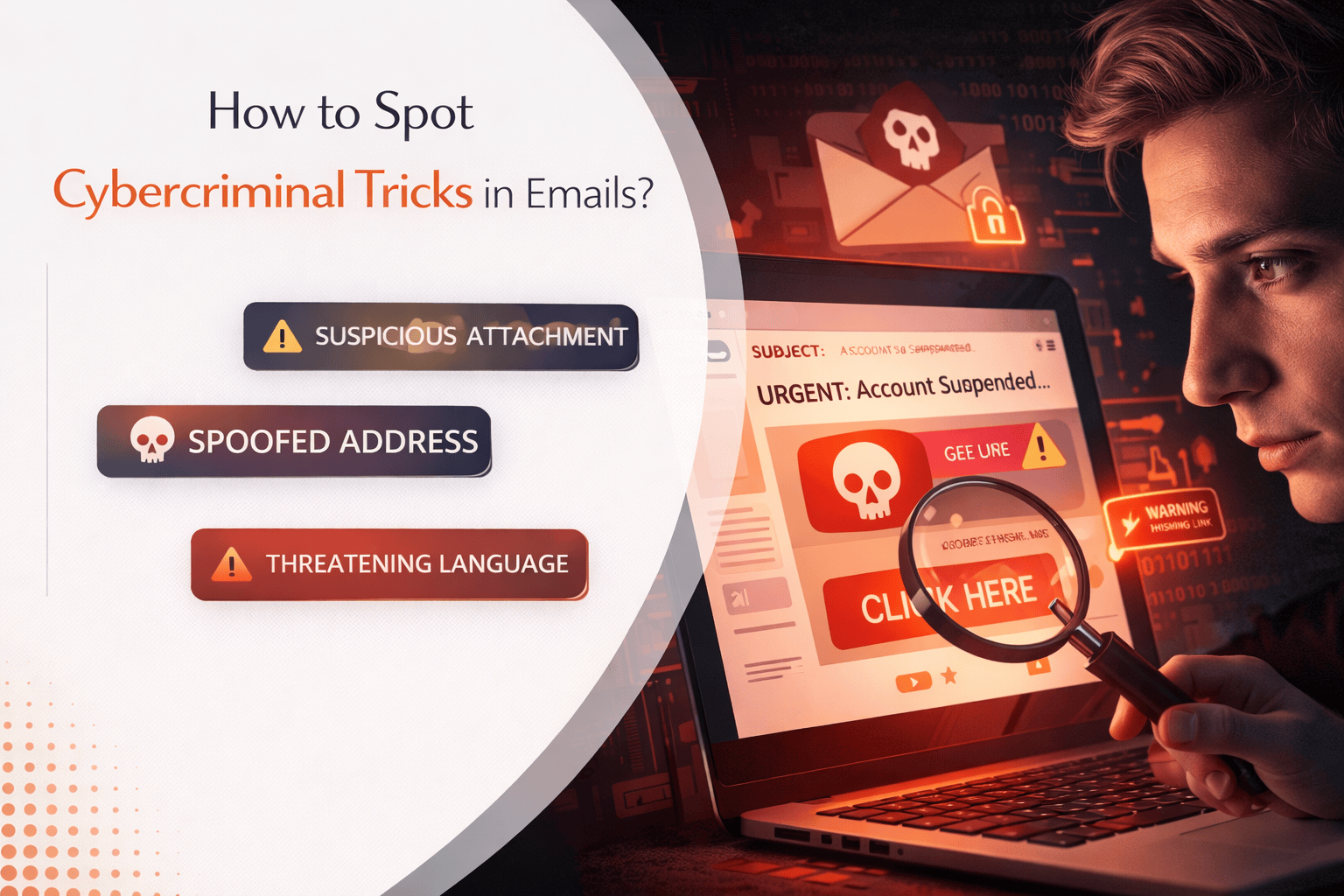
Common Cybercriminal Email Tactics to Watch For
Recognizing patterns in malicious emails is the first step toward prevention. Below are the most frequently used tactics:
1. Urgency and Pressure
Emails that create a sense of urgency - such as “Your account will be suspended” or “Immediate action required” - are designed to bypass rational thinking. Attackers want recipients to act quickly without verifying authenticity.
2. Spoofed Sender Addresses
Cybercriminals often disguise email addresses to appear as trusted sources. This may include slight variations in domain names or display names that mimic legitimate organizations.
Example:
support@micros0ft.com instead of support@microsoft.com
Always check the full email address, not just the display name.
3. Malicious Links and Attachments
Phishing emails often include files that install malware or links that take users to phony login sites. At first sight, these connections might seem authentic.
Best Practice:
To confirm the destination URL, hover over links before clicking.
4. Social Engineering and Personalization
Modern attacks use publicly available data to personalize emails. Attackers may reference your company, role, or recent activity to build trust.
This technique is especially common in spear phishing and B2B-focused attacks.
5. Fake Invoices or Payment Requests
Business email compromise (BEC) attacks often involve fraudulent invoices or payment instructions. These emails may appear to come from vendors, partners, or even senior executives.
Always verify financial requests through a secondary communication channel.
How to Protect Yourself and Your Organization
Preventing email-based cyberattacks requires a combination of awareness, technology, and process-driven safeguards.
Key Prevention Strategies:
- Verify before you click: Always confirm the legitimacy of emails requesting sensitive actions.
- Turn on multi-factor authentication (MFA): It increases security.
- Use advanced email filtering solutions: Detects phishing attempts and malicious attachments.
- Train employees regularly: Human awareness is the first line of defense.
- Report suspicious emails immediately: Early detection can prevent larger breaches.
Organizations that invest in cybersecurity awareness programs significantly reduce their risk exposure.
The Role of Cybersecurity Awareness in 2026
As cyber threats evolve, so must defense strategies. AI-driven phishing attacks, deepfake communications, and automated social engineering campaigns are making detection more challenging.
Cybersecurity is no longer just an IT responsibility - it is a business-wide priority. Employees at every level must be equipped to recognize threats and respond appropriately.
Final Thoughts
Cybercriminals are constantly refining their tactics, but many attacks still rely on simple human errors. By understanding how malicious emails are crafted and adopting proactive security measures, individuals and organizations can significantly reduce their vulnerability.
Staying alert, verifying communications, and building a culture of cybersecurity awareness are critical steps in defending against modern email threats.
In a digital-first world, the ability to spot cybercriminal tricks isn’t just a skill - it’s a necessity for protecting data, systems, and business continuity.